How to get started with compliance and risk management on your team
No cloud-native application is immune from risk. One could argue that by merely deciding to build in the cloud, you are exposing yourself and any future customer data to potential threats. Compliance risk management practices exist to minimize your exposure to security incidents and ensure compliance with required standards. This guide walks you through the various tools and methods utilized by small and mid-size businesses to build in compliance from the ground up.
What Is Compliance Risk?
Compliance risk is defined as any vulnerability that prevents you from remaining compliant with established security standards, such as SOC 2, PCI DSS, or HIPAA. These vulnerabilities include limited or incorrect security controls, as well as non-existent or weak protocols or policies around compliance standards. Unaddressed compliance risks expose you to penalties should you fail an audit, but they also expose your customer and internal information and systems to malicious actors. For these reasons, compliance risk management is an important consideration for all developer teams.
Tools for Compliance Risk Management
These three types of documents are widely used to document, track, and manage compliance risks:
- Compliance risk management framework: A document that lays out your compliance management governance (who is responsible for which aspects of the compliance process) and an accompanying set of steps to manage different types of risk. Many organizations choose to use the COSO EMR framework or the ISO 31000 framework as the foundation and add on components that make sense for their industry. A standard framework includes risk identification; risk measurement and assessment; risk mitigation; risk reporting and monitoring; and risk governance.
- Compliance risk assessment templates: Customizable pre-built documents typically included in compliance management software that summarize your organization’s risk profile, including security gaps and remediation plans.
- Compliance management system: A software solution that, as the name implies, helps teams document, track, and manage their compliance efforts. Most CMS worth their salt will also integrate with popular developer tools like Jira as well as any project management systems you use in order to make compliance documentation a seamless, automated process.
Want to learn more about compliance risk? Read How to Manage Compliance Risk: 3 Tools for Effective Mitigation next.
Defining Compliance Programs
A compliance program is a set of protocols and procedures that dictate how your team manages (or will manage) compliance requirements. Even if your product is yet to hit the market, your team needs a compliance program in place in order to avoid delays and various pitfalls right before the live date. Having a roadmap in place helps with accountability, clarity, and can ultimately get you to market faster. By having all of your documentation together, you’ll be better prepared for audits and simultaneously give your product a better chance at a passing score, all of which speeds up the security review process.
Elements of Successful Compliance Programs
Most top-notch compliance programs have some of these elements in common:
- DevSecOps approach: Developer teams that collaborate with operations and security professionals every step of the way tend to get better compliance results by building in required security standards throughout the entire development lifecycle.
- Comprehensive documentation process: Having good documentation that can prove compliance wins half the battle when it comes to passing an audit, which is why the best compliance programs stipulate how, when, and who is responsible for documenting processes.
- Built-in automation: Automated scans, reminders, integrations with other key platforms, and reporting tools make following a compliance program easier. Consider thinking through and adding an arsenal of tools to your compliance program document.
- Accountability: A significant component of any compliance program document is governance. Your team should know exactly who in your organization is responsible for various aspects of compliance as well as any remediation efforts.
Ineffective compliance programs, unsurprisingly, have the opposite elements of the ones described above. Teams that work in silos, rush or don’t take time to develop a process for compliance at all, often end up stuck in lengthy security reviews, with failed audits and a laundry list of remediation measures they need to take before their product can go live.
Tips for Starting a Compliance Program
Your compliance program should be tailored to the needs of your team and product specifications, but some common sense best practices apply:
- Know which security standards apply to your product: In the US, most companies will need to comply with SOC, PCI DSS, GDPR, CCPA, and/or HIPAA before going to market.
- Set compliance milestones: “To achieve compliance in X standard” is a broad goal, and may feel as attainable as reaching the moon. Breaking down the various components into manageable chunks lets your team incorporate compliance tasks into their day-to-day, which leads to consistent progress.
- Create a toolkit: As mentioned earlier, knowing which tools you’ll use to achieve compliance ahead of time can set you up for a less stressful time during the audit process.
- Document goals and processes: Store compliance documents and policies in an accessible yet secure place where team members can reference them anytime they run into an issue or are not sure where to turn for help.
To dive deeper into what makes a successful compliance program read What Is a Compliance Program?
What Is a Compliance Management System?
A compliance management system (CMS) is a software solution that helps developers plan, schedule, automate, track, and manage compliance-related tasks. Its primary purpose is to make compliance risk management less burdensome for busy DevOps teams. While chief compliance officers (CCOs) and your board of directors are responsible for compliance decisions, the everyday tasks associated with securing your systems lie with individual contributors, and this is where an effective compliance management system is useful.
Key Features of Compliance Management Systems
- Risk management: A CMS should be able to scan and test security features on a weekly or monthly basis and then issue reports, ideally with remediation suggestions. In other words, it should automatically do tedious tasks that would take away valuable time from the brilliant humans on your team.
- Audit management: Whether it’s automated reminders for important milestones or a tool for documentation management, your CMS should make audit time easier for your team.
- Integrations: The best CMSs integrate with your developer tools and project management software so communication between teams is seamless and new features are not excluded from the compliance workflow.
- Intuitive workflow: Though a CMS is used by developers, one should not have to know code in order to use it. Product managers and your administrative team should be able to log and view appropriate documentation in the CMS without extensive training or specialized knowledge.
Tools for Compliance and Risk Management
DuploCloud
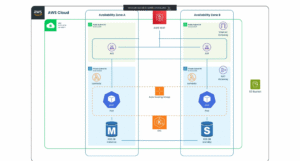
DuploCloud provides a continuous compliance automation platform. DuploCloud is built on DevSecOps principles and is pre-built with many of the most commonly required security controls. Using the platform can help small and mid-size companies who are building cloud-native applications take their products to market faster. Most of the compliance tasks that would normally need to be completed by your developer or DevOps team are done for you and updated automatically so you can focus on the features that make your solution unique.
Hyperproof
In addition to being a compliance automation platform, Hyperproof allows you to schedule and track compliance tasks, as well as forecast updates and upcoming audits.
RiskCloud by Logic Manager
While RiskCloud is primarily an assessment solution, it also has features for compliance and risk management, including policy documentation, reporting, and helping teams align their protocols with common standards like ISO and GDPR.
Want to know more about compliance management systems? Read What Is a Compliance Management System? next.
Managing Compliance Audits
For teams building cloud-based applications, compliance management is a never-ending process punctuated by compliance audits. There are a few different kinds of audits you’ll potentially need to participate in, though your requirements will vary depending on the industry your application serves and the kinds of services it provides.
Types of Compliance Audits
There are many different types of audits, but these four are the most common for cloud-based applications:
- Health Insurance Portability and Accountability Act (HIPAA): A HIPAA audit tests how well your systems protect the personal health information of customers and employees, both when storing and transmitting data. HIPAA applies to a wide range of companies that are not directly related to healthcare, including software providers for beauty businesses and insurance companies.
- Payment Card Industry Data Security Standard (PCI DSS): These audits test how well your systems protect credit card information. Since most businesses accept some form of credit card payment, you will likely need to achieve some level of PCI DSS compliance.
- Sarbanes-Oxley Act (SOX): This type of audit evaluates the accuracy of public company financial statements and makes sure businesses implement disaster recovery measures, such as electronic communications backups.
- System and Organization Controls 2 (SOC 2): One of the most common audit types for cloud-based applications, SOC 2 audits ensure your organization meets basic security standards that protect consumer information.
Steps in a Compliance Audit
The steps will vary by audit type, but generally most will follow this workflow:
- Initial meeting with auditors: Your company leaders will engage and meet with the auditor who may provide you with a compliance checklist. At this time the leadership and the auditor will formally agree on the type of documentation required and which parts of the company will be audited, as well as specific timelines.
- The audit: During this time, auditors will go through documentation and may ask to observe your workflows, internal controls, and employee adherence.
- Audit report: Once the observations are complete, the auditor will compile a report with recommendations and a determination of whether or not you’re meeting the required security standards. If infractions are minor, you may have the opportunity to remedy them within a specified amount of time and still earn a passing score.
Generally, senior leadership is responsible for overseeing remediation efforts, which are broken up into different milestones and then assigned to relevant teams and individual contributors.
When Do Audits Take Place
Most audits take place when a company is preparing to take a new product to market and wants to prove that its security protocols meet required standards or as part of ongoing annual compliance. However, an audit from any of the governing bodies can also take place following a security breach, a fraud incident, or by chance.
- HIPAA: The Office for Civil Rights conducts audits of a random selection of health organizations every year. An employee can also file a complaint if they observe violations, which can trigger an audit.
- PCI DSS: Most PCI DSS audits are initiated by companies that want to remain compliant, but they can be mandated after a breach event.
- SOX: Publicly traded companies are required to submit to audits on an annual basis.
- SOC 2: Annual edits are required for companies that want to remain compliant and have up-to-date SOC 2 reports to share with potential clients.
Penalties for Failed Audits
Not all failed audits are created equal; some may carry an opportunity to create stronger security protocols, especially if your product is not yet on the market. Falling out of compliance and experiencing a security event will usually be more damaging to your reputation and may come with financial penalties.
- HIPAA: Penalties depend on the severity of the violation, but tend to range from $100 per violation to $50,00 per violation.
- PCI DSS: You may be fined up to $500,000 per incident of breach by payment card companies.
- SOX: If you knowingly submit a report that doesn’t meet SOX Act standards, you may be liable for a fine of up to $1 million and up to 10 years in prison. Willfully certifying a report that fails SOX standards with a clear intent to mislead can result in a fine of a maximum of $5 million and a prison sentence maximum of 20 years. You may also be delisted from stock exchanges.
- SOC 2: While there are no financial penalties involved, failing a SOC 2 audit, especially following a security incident, can damage your reputation and business. SOC 2 is an industry standard, and the majority of cloud-based applications are expected to provide evidence of compliance to clients.
To learn more about compliance audits, read What Is a Compliance Audit?
Achieving Compliance With Public Cloud Vendors
Most small and mid-size businesses building in the cloud take advantage of compliance tools provided by third-party public cloud vendors. Since the market is currently dominated by the big three: Amazon Web Services, Microsoft Azure, and Google Cloud Platform, you will most likely encounter these providers on your journey to compliance.
Amazon Web Services (AWS)
If you’re using AWS as your cloud provider, you can take advantage of the extensive library of third-party attestations and certifications provided, which can save you time in recreating validation paperwork when demonstrating compliance in AWS’ IT environment. Amazon offers two ready-to-deploy frameworks to its customers including the Landing Zone Accelerator on AWS and Verifiable Controls Evidence Store.
General Resources in AWS
Start by reading the Amazon Web Services: Risk and Compliance whitepaper to get a general sense of AWS compliance offerings. Note that while AWS doesn’t require its customers to follow a specific set of operations to achieve compliance, it does recommend the AWS Well-Architected Framework as a foundation. It also features a list of resources for those who want to pursue Cloud Security Alliance Security Trust Assurance and Risk (CSA STAR) certification.
Regional Resources in AWS
For businesses working in the financial sector, AWS offers a filterable list of over 60 countries, with information on which governmental bodies manage financial businesses, as well as key data privacy and protection regulations. Similarly, for healthcare and healthcare-adjacent AWS offers a country-by-country breakdown of global certifications and accreditations such as HIPAA, HITRUST, and GDPR. Meanwhile, SOC reports and ISO 27001 certification information can also be found on the AWS site.
For more information about compliance in AWS, read How to Achieve Compliance in AWS.
Microsoft Azure
General Compliance Resources in MS Azure
MS Azure customers worldwide have access to:
- Azure Blueprints which groups access controls, policies, and other templatized configurations within one blueprint definition. It also has built-in sample templates which adhere with common standards such as SOC 2.
- Microsoft Defender for Cloud, which conducts continuous security assessments of multi-cloud and hybrid environments.
- Azure Policy which enables real-time enforcement of policies via guardrails, which will automatically govern current and future resources and provide remediation.
Global and Regional Compliance in MS Azure
MS Azure divides its resources into global, region-specific, and industry-specific.
- Global: CSI benchmarks, CSI STAR, ISO, SOC, WCAG
- US government: DFARS, DoD impact levels, EAR, FedRAMP, StateRAMP
- Industry-specific: FERPA, FINRA 4511, HIPAA, HITRUST, NERC
For a more complete list of MS Azure compliance service, give How to Achieve Compliance in Azure a read.
Google Cloud Platform (GCP)
GCP’s compliance offerings are listed in its vast compliance center, though customers may want to read the Trusting Your Data with Google with Cloud whitepaper beforehand to get an idea of Google’s stance on compliance and privacy. Google organizes its compliance resources similarly to AWS and MS Azure, addressing security standards on global and regional levels.
General Compliance Resources in GCP
Customers can download templates and Google’s certifications from third parties from the compliance report manager, making it easier to gather documentation before audits. You also get access to Google’s Cloud Identity and Access Manager and Cloud Data Loss Prevention tool, which walk companies through securing data stored on the cloud.
Resources for US Customers
GCP provides compliance tools for all common security standards required in the US, including HIPAA, SOC 2, PCI DSS, and CCPA.
To learn more about GCP, read How to Achieve Compliance in GCP.
Continuous Compliance with DuploCloud
DuploCloud serves as a continuous compliance tool and launch pad for small and mid-size teams building in the cloud. Our built-in controls are compliant with common regulatory standards (SOC 2, HIPAA, and PCI DSS, among others) out of the box, which allows your team to perfect your application with a solid foundation already under their feet. Schedule a demo to learn more about our platform.