Achieve and Maintain SOC 2 Compliance with DuploCloud
SOC 2 compliance is a set of internationally recognized data security, privacy, and transparency standards vital for businesses handling customer data. DuploCloud's DevOps automation platform streamlines and enhances your SOC 2 compliance processes, meeting strict security requirements while transforming compliance from a burden into a strategic advantage.
Get started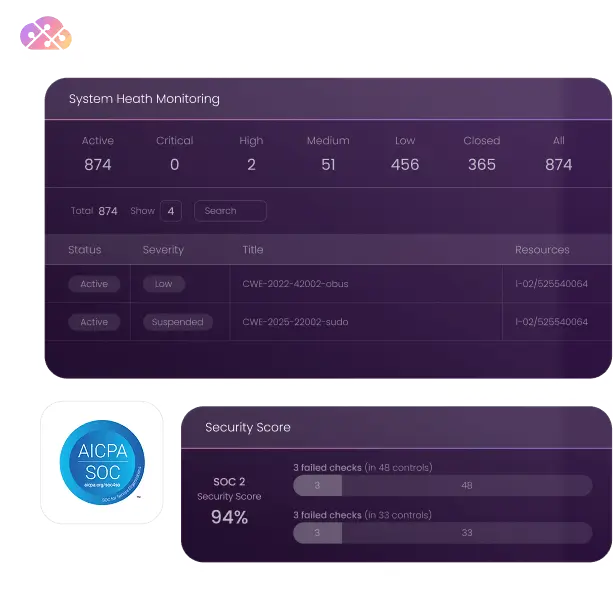
Key Features
Achieving and maintaining SOC2 compliance can be a complex process involving multiple teams and systems. DuploCloud simplifies this process by providing a framework that automates most manual tasks to get your business compliance-ready. Our platform also automates data management, system updates, and access controls, reducing the chance of human error.
Security is a key component of SOC 2 compliance, and DuploCloud is committed to helping you protect your sensitive data. Our platform provides robust security features, including encryption, secure access controls, and regular system updates. These features help safeguard your data against potential threats, ensuring that your organization meets the stringent security requirements of SOC 2 compliance.
DuploCloud serves as a partner that monitors your compliance status 24/7. Our platform provides real-time alerts and updates, allowing you to act promptly to maintain your compliance status without constant manual checking.
DuploCloud’s detailed reporting and logging simplify audit preparation. Our platform logs all relevant activities and generates comprehensive reports, providing auditors with the information they need in an accessible format. This saves time and effort and effectively demonstrates compliance, fostering stakeholder trust.
Frequently Asked Questions
DuploCloud helps simplify compliance processes, provides continual compliance monitoring, enhances security, and streamlines audits. It reduces the chance for human error and frees up resources for strategic tasks.
DuploCloud implements robust access controls in its tenant model, including identity and authentication management using IDPs like Gsuite and O365, and network segmentation. It employs instance profiles and managed identities to limit access to AWS and Azure resources, ensuring secure and compliant access.
DuploCloud orchestrates encryption for data at rest and in transit using services like AWS KMS and Azure Key Vault. It also manages encryption keys securely, aligning with SOC2 requirements for data protection.
DuploCloud integrates with Wazuh, a third-party SIEM solution, to monitor compliance and vulnerabilities. It provides infrastructure scanning, file integrity monitoring, and utilizes ClamAV for malware detection, ensuring ongoing compliance and security monitoring in line with SOC2 standards.
Resources
10 IaC Tools for DevOps Professionals
10 Prompts Every Engineer Doing DevOps Should Know
Industry leaders choose to
Build with Duplo
Join hundreds of enterprises managing their cloud infrastructure with Duplo. Clear your DevOps backlog and save operational costs.


