Simplify Your HIPAA Compliance Journey with DuploCloud
Health Insurance Portability and Accountability Act (HIPAA) compliance is critical for businesses in the healthcare sector dealing with Protected Health Information (PHI). The requirements landscape can be intricate and daunting, but DuploCloud transforms this challenge into an effortless process. Our solution eases HIPAA compliance, ensuring your healthcare data is secure, your processes streamlined, and your business ready to face the demands of the healthcare industry confidently.
Get Started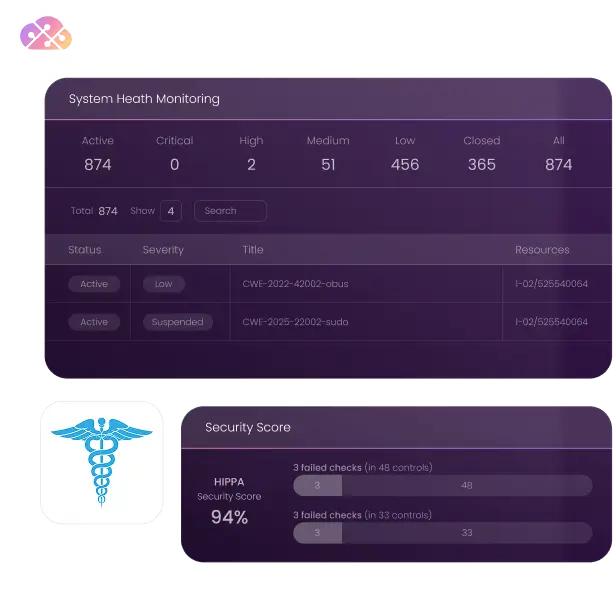
Key Features
DuploCloud’s platform simplifies HIPAA compliance by automating the intricate steps involved. It conducts regular checks and continuous monitoring, reducing manual workload and mitigating the risk of human error, thereby ensuring a streamlined path to compliance.
With advanced security controls in place, DuploCloud creates a strong line of defense for your Protected Health Information (PHI). It actively minimizes the potential for data breaches, helping you maintain regulatory compliance while building trust with patients and partners.
DuploCloud’s comprehensive dashboard gives you a detailed, real-time view of your security posture. This centralized overview enables swift identification and mitigation of potential risks or compliance gaps, fostering an environment of proactive rather than reactive security management.
The platform continuously audits your cloud infrastructure against HIPAA requirements. This constant vigilance ensures that you consistently meet regulatory standards, providing you with peace of mind and freeing your team to focus on other strategic initiatives.
DuploCloud stays ahead of the regulatory curve by updating your systems in line with any changes or updates to HIPAA requirements. This proactive approach ensures that your infrastructure remains compliant, even as regulations evolve.
DuploCloud automatically encrypts your data and backs it up, providing an additional layer of security. This feature not only safeguards your data but also helps to maintain its integrity and accessibility, which are key elements of HIPAA compliance.
Frequently Asked Questions
DuploCloud keeps up-to-date with changes in compliance regulations by using a dynamically-updated rules database. This database constantly monitors and updates the environment according to the latest compliance and security standards. Users are notified of any variances in compliance and security standards, which are assigned severity priorities. This allows users to address and update their environment at their convenience.
DuploCloud uses encryption for data at rest and in transit to protect ePHI. It orchestrates KMS keys per tenant for encrypting various AWS resources like RDS DBs, S3, Elastic Search, and REDIS. For data in transit, DuploCloud uses certificates from Cert-Manager to enable TLS encryption, ensuring the protection of ePHI as per HIPAA guidelines.
DuploCloud maintains comprehensive audit trails in addition to AWS CloudTrail, logging all write events about infrastructure changes in an ELK cluster. It also employs the Wazuh agent to track activities at the host level, with CloudTrail, audit, and Wazuh agent events consolidated in the Wazuh dashboard. This fulfills HIPAA’s requirements for regular review of information system activities.
DuploCloud’s tenant model implements strict access controls, allowing access based on user roles. This mechanism integrates into the VPN client, ensuring that each user’s access is appropriately restricted. By default, no access to a tenant is allowed unless specific ports are exposed via an elastic load balancer, aligning with HIPAA’s requirements for safeguarding access to ePHI.
DuploCloud’s infrastructure is designed with multiple availability zones to ensure resilience and continuity in case of emergencies or system failures. This setup allows for the dynamic transfer and resumption of system operations, ensuring the protection and accessibility of ePHI even in emergency modes, as required by HIPAA regulations.