This costly standard can be a difference-maker for potential clients
Demand for SOC 2 compliance has proliferated over the last few years as businesses become more concerned with cloud safety. High-profile hacks such as those at Microsoft, Samsung, and the Los Angeles Unified School District have shown that bad actors are constantly on the prowl for vulnerabilities they can exploit, and anywhere sensitive data is stored can become a target. SOC 2 compliance ensures a level of security in your systems that will both protect them from breaches and assure clients that they can trust your business.
But what is SOC 2 compliance, exactly? How do you achieve it? How are SOC 1 and SOC 2 compliance different? Who needs SOC 2 compliance? And what does it all cost? Read on to find the answers.
What Is SOC 2 Compliance?
SOC 2 is a set of standards for cloud computing programs and software-as-a-service companies developed in 2010 by the American Institute of Certified Public Accountants (AICPA) to protect customer data. SOC stands for System and Organization Controls, and SOC 2 focuses differently than SOC 1 (more on that later). This compliance requires receiving a passing grade from a certified SOC auditor. To pass, a business must adequately address the appropriate components of the five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
The Five Trust Services Criteria
Each of the five Trust Services Criteria has a specific purpose, but a business seeking SOC 2 compliance need not address all five. Beyond security — which is all but mandatory for any business, regardless of industry — a business need only address those criteria relevant to the product or service it offers. For example, a medical business mindful of HIPAA would need additional safeguards against non-relevant employees accessing patient records. That would mean increased attention to the Confidentiality criterion.
Here’s what each of the Trust Services Criteria focuses on:
- Security: The protection of system resources against unauthorized access, system abuse, data theft, software misuse, and improper alteration or disclosure of information.
- Example measures: two-factor authentication and intrusion detection systems.
- Availability: The accessibility of the system, product, or service as stipulated by a contract or service level agreement.
- Example measures: performance monitoring, disaster recovery, and incident handling protocols.
- Processing Integrity: Whether or not the system achieves its purpose, delivering the right data at the right time.
- Example measures: quality assurance and processing monitoring.
- Confidentiality: The restriction of data access or disclosure to a specified set of people or organizations.
- Example measures: encryption and access controls.
- Privacy: The collection, use, retention, disclosure, and disposal of personal information according to AICPA’s generally accepted privacy principles (GAPP).
- Example measures: encryption, access control, and two-factor authentication.
To determine which Trust Service Criteria you need to focus on, it can be helpful to perform a SOC 2 readiness assessment. We’ll get into the details of that process below.
The Two Types of SOC 2 Audits
Two types of SOC 2 audits are Type I and Type II. The difference between the two audits lies in the length of time over which the audit takes place. SOC 2 Type I audits evaluate your business’ controls at a single point in time. They essentially examine the design of your controls with the five Trust Service Criteria in mind and determine whether or not that design should adequately meet those criteria.
What Type I audits do not address is how those controls function in practice. A Type II audit widens the scope to evaluate controls over a 3-12 month period, assessing control design and effectiveness. Although they are more costly and time-consuming, Type II audits have become the industry standard because they assure both businesses and their customers that the controls are working as designed.
Whichever SOC 2 audit type you choose for your business, you must repeat it every 6-12 months to demonstrate continued customer compliance.
What Is the Difference Between SOC 1 and SOC 2 Compliance?
SOC 1 and SOC 2 compliance differ in their scope: SOC 1 compliance focuses solely on financial controls, while SOC 2 addresses adherence to all five Trust Service Criteria across a business. Both stem from the Statement on Standards for Attestation Engagements (SSAE) 18, but each addresses a different section. SOC 1 addresses section AT-C 320, whereas SOC 2 addresses sections AT-C 105 and AT-C 205.
That means SOC 1 is intended primarily for revenue software organizations. It covers an organization’s controls as they pertain to its customers’ financial statements, detailing whether or not that organization’s financial controls meet its objectives. If a service directly affects the financial reporting of its users, it likely needs a SOC 1 audit rather than SOC 2.
On the other hand, SOC 2 compliance casts a wider net, moving beyond financials to address the five Trust Service Criteria. It aims to ensure customer data of every kind is properly protected and is especially important for SaaS providers and other cloud service platforms.
Ready to take your understanding of SOC 2 Compliance further? Check out The Complete Guide to SOC 2 Compliance.
Who Needs SOC 2 Compliance?
Any service organization that stores, processes, or transmits any kind of customer data using the cloud would likely benefit from SOC 2 compliance. SOC 2 isn’t a regulatory standard, but it has become the de facto standard in the cloud computing industry.
Healthcare businesses benefit from SOC 2 compliance because privacy, security, and confidentiality are all major concerns in the field. Although HIPAA standards cover protected health information, SOC 2 can provide additional assurance to customers that their information will be safely maintained.
Financial industries such as banking and cryptocurrency frequently pursue SOC 2 compliance because they need to keep customers’ information safe. The trust between a financial institution and its customers may be that company’s most important asset, and SOC 2 compliance underscores its commitment to safeguarding that trust. Businesses dealing in cryptocurrency are especially vulnerable to trust violations because of the volatility of the industry and its frequent targeting by bad actors, making SOC 2 all the more attractive for business owners.
Education institutions store a wealth of protected information regarding faculty and students. There are strict regulations regarding student information protection, and a successful SOC 2 audit can ensure those regulations are being met.
Are you SOC 2 compliant? SOC 2 is one of the most respected cybersecurity frameworks that service providers can be certified in, and our free checklist will walk you through each step:

Technology and software-as-a-service companies can be particularly vulnerable to cyber attacks, which are costly, legally troublesome, and reputationally damaging. Meeting SOC 2 requirements can prevent such a breach; the earlier a business dedicates itself to security, the more deeply that practice is woven into the fabric of the business.
How Do I Get SOC 2 Compliance?
Now that you’ve determined you need SOC 2 compliance, you’ll have to go through the potentially arduous process of actually acquiring certification from an auditor. But there are still decisions to be made and costs to measure. We’ll guide you through.
Type I or Type II Audit?
The first call you’ll need to make when seeking SOC 2 compliance is whether you want to pursue a Type I or Type II audit.
Generally speaking, Type II has become the standard for cloud services. It’s what customers want to see when they peruse your security offerings. However, a Type I audit can serve as a stopgap while you wait the 3-12 months a Type II audit typically takes.
Identifying and Filling Gaps in Security and Documentation
With an understanding of the five criteria in mind, you can have your technical team put together the necessary documentation. You could take the resulting information and go directly to the auditor who will conduct your SOC 2 audit, or you could hire that auditor (or a SOC consultant) to prepare a readiness assessment. They will examine what you’ve produced and compare it to SOC 2 standards, producing a gap analysis you can use to make your business as SOC 2 audit-ready as possible before committing to the lengthy process.
You may balk at spending for a readiness assessment and gap analysis, but remember that spending on these steps now could save you from failing your SOC 2 audit. That would mean even more time and money spent playing catch up, all the while losing potential business customers that would be happy to work with you had you achieved SOC 2 certification.
Select an Auditor and Begin
Any licensed CPA can perform the SOC 2 audit, but you’ll want to seek out one that specializes in SOC 2 compliance to ensure you receive a quality report. You should also consider your auditor’s level of experience, timeliness, whether or not they offer a readiness assessment, and how much they cost. Standard practice is to undergo a SOC 2 audit once every 6-12 months even after passing your first audit, so costs can add up quickly. Speaking of which…
What Does SOC 2 Type II Compliance Cost?
SOC 2 Type II compliance costs can total between $30,000 and $220,000 depending on the size of your firm, the scope of the audit, and the experience of the CPA firm you enlist. Companies tend to budget around $100,000 and several months of work when pursuing a SOC Type II audit from start to finish, and should expect a substantial amount of lost productivity over the course of the audit.
Before the Audit
SOC 2 costs begin well before the audit. If you play it safe and opt for a readiness assessment done by SOC professionals, it will cost you an estimated $15,000. Once you’ve done that, you’ll need to address the shortcomings revealed in the gap analysis, which could mean buying new tools, training employees on their use, and maybe even hiring additional employees to operate them. One CTO estimated lost productivity from his SOC 2 Type I endeavor at between $50,000 and $75,000, and a Type II evaluation would cost as much or more. Hiring the firm that performed your readiness assessment to help close gaps, on the other hand, could cost between $25,000 and $85,000, depending on the size of your company and the complexity of its systems.
During the Audit
The cost of the audit itself can vary widely depending on the number of Trust Services Criteria deemed relevant to your organization. The size of your company also plays a hand in determining audit costs. All told, you can expect to pay anywhere from $30,000 to $60,000 for the audit itself.
You’ll also have to account for lost productivity among key members of your team during the audit. Engineering leads, human resources, and senior management will all likely find themselves tied up in meetings with the auditors, remediating any issues they discover, and chasing down documentation across the business.
After the Audit
Although SOC 2 Type II compliance doesn’t officially expire, the assessments themselves typically build in around one year of validity. Beyond that 12-month mark, the assessment becomes outdated. As a result, many businesses opt to renew their SOC 2 Type II compliance every 6-12 months.
Successive audits should require fewer expenses around tools, training, and lost productivity, but they’ll still require the auditing firm to return and receive payment for its time.
How Can DuploCloud Help with SOC 2 Compliance?
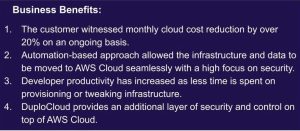
DuploCloud’s platform offers automated provisioning and orchestration across network, compute, storage, containers, cloud native services, and CI/CD, with continuous compliance and 24/7 monitoring controls plus support from certified experts.
The platform comes with a huge number of SOC-compliant controls targeting the five Trust Service Criteria. We provide necessary security features such as data encryption, role-based access controls, antivirus and anti-malware software, performance monitoring, capacity forecasting, data backup, and more. That saves you time and money on building tools addressing the Trust Service Criteria, and helps streamline certification during the audit process.
We also provide all the documentation on our controls that you’ll need for the audit. Our toolset comes with sample auditor- and customer-ready information security and infrastructure security documentation that you can then adjust to meet your company’s specific needs. They include proof of security controls, operational reports, and corroborating screenshots of the controls in action.
To learn more about the ways DuploCloud can make SOC 2 certification easier, read our white paper.